#1 Most Trusted Name in Web3 Security
At Ledger Enterprise, our priority is security. That’s why we offer the industry’s most scalable solution to protect and safeguard your company’s digital assets with easy-to-use governance.





.avif)
Personal Security Devices
Don’t trust, verify. With our hardware-first approach, every single transaction is verified with Clear-Signing technology.
Eliminate risk of malicious attacks, collusion or negligence with What You See What Is You Sign (WYSIWYS).







.png)


Ledger Security, at Scale
Enjoy the industry’s most secure solution without having to sacrifice usability, speed or scale.
Our end-to-end solution combines Ledger’s proprietary hardware, firmware and software security stack with flexible governance and a best-in-class insurance program.



Exchanges
Achieve unmatched scalability and efficiency with automation, advanced reporting, and audit trails. Simplify wallet and fleet management while protecting assets with industry-leading technology, transaction clearsigning and hardware-enforced governance.





Custodians
Take full control of digital assets with true self-custody, enabling unmatched security and flexibility. Expand your offerings with services like off-exchange trading, all backed by best-in-class hardware security and seamless operation management.





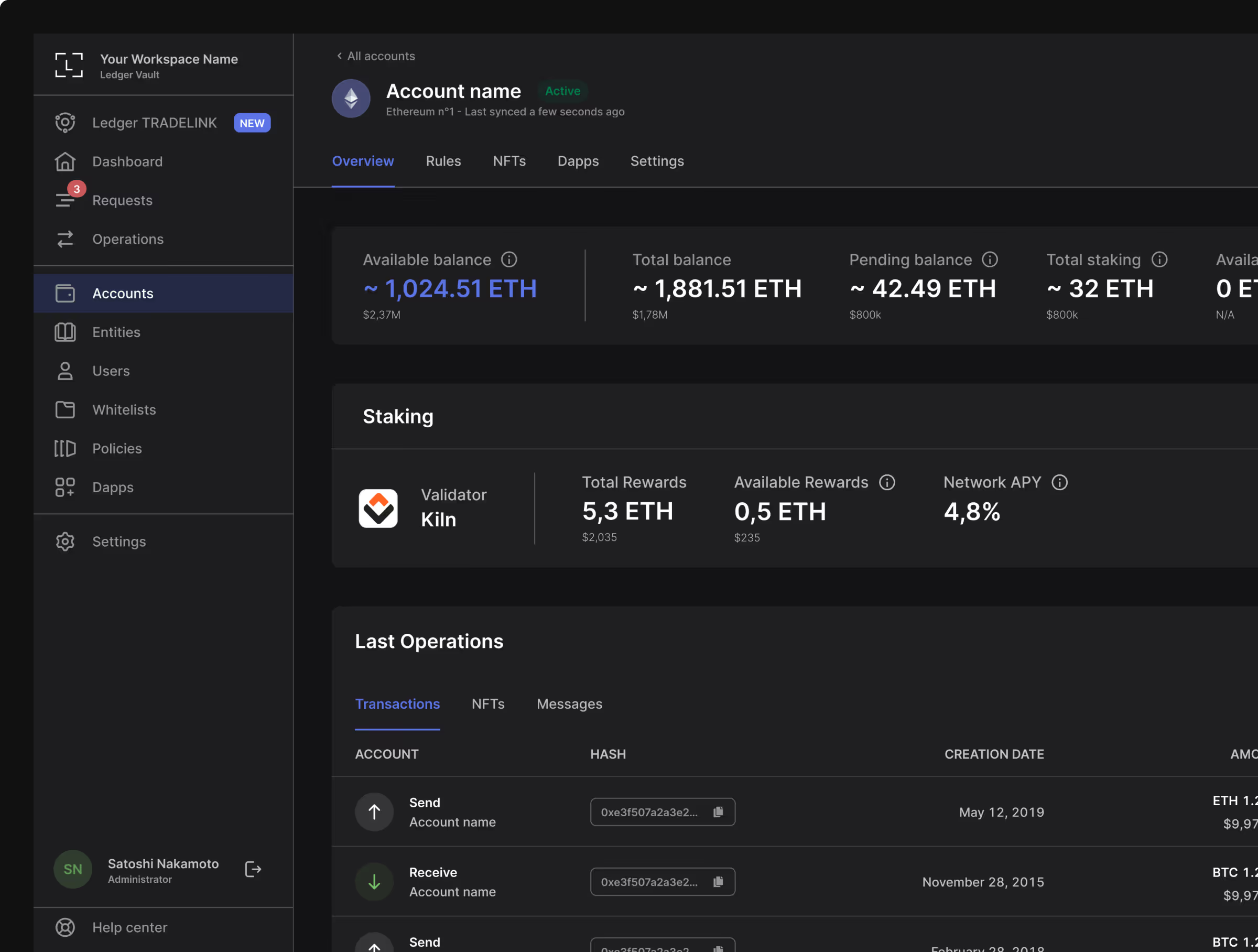
Assets Manager
Effortlessly navigate Web3 with secure, intuitive tools for treasury management, staking, trading, tokenization, and more. Maintain full control with robust backup options and Web3 checks, ensuring seamless portfolio management and complete peace of mind.


Proprietary Operating System
Ledger’s proprietary OS is used in all Ledger devices, providing powerful protection against a number of threats.
Additionally, Ledger protects digital value in a FIPs level III hardware ecosystem, which is the same technology used by governments and international banks.





Hardware Security Modules
Hardware Security Modules (HSMs) are the second part of Ledger’s unique hardware based security architecture.
Making sure your customized governance rules are met before validating your transactions on the blockchain.
• FIPS level III
• Proprietary hardening
• Cluster infrastructure
• EAL5 + certification
Insurance Policy
Because peace of mind comes with guarantees, Ledger Enterprise created a turn-key Specie insurance program underwritten by Arch Insurance (UK) Limited.
Through this Specie program, you can easily set up a custom policy as an add-on and reach groundbreaking insurance, with some of our clients covering up to $750 million.



Personal Security Devices
Don’t trust, verify. With our hardware-first approach, every single transaction is verified with Clear-Signing technology.
Eliminate risk of malicious attacks, collusion or negligence with What You See What Is You Sign (WYSIWYS).
.png)


USD Billions in transactions, ZERO mismanaged.
Ledger Enterprise Operates since
2019 with 0 hack or asset lost.
Frequently Asked
Questions


.svg)



Your Partner
in Web3
Request a 30-minute meeting to discover how Ledger Vault can keep your business and your crypto safe.







.avif)









